It Security
Q Tbn 3aand9gct9zgofihqfieo8juo8ro68yxwhhptcbiazdw9ijtnnvciipyt2 Usqp Cau

It Security Nasa

10 Cyber Security Tips Fro Small Business Pentucket Bank

It Security Consultant Learning Paths Explored

The Rising Pressure To Invest In More It Security Talent Talent Germany

4 It Security Best Practices Smbs Need To Adopt Immediately Bytestart


Methods For Easing Your Top Cyber Security Challenges Channel Futures
12 Things Every It Security Professional Should Know Cso Online

10 Steps To Define Your Cyber Security Strategy Cybriant

Why Is Cyber Security Important It Company Birmingham
It Security

It Compliance Vs It Security What S The Difference Bmc Blogs

8 It Security Processes To Protect And Manage Company Data Process Street Checklist Workflow And Sop Software

Cyber Security Strategy Solutions Conet De

Council Post 10 Cybersecurity Protocols Every Tech Professional Should Follow

Managed It Services Vs Managed Cyber Security Services Explained Empower It Solutions

It Security Refresh The Cyber Defense Matrix No Jitter

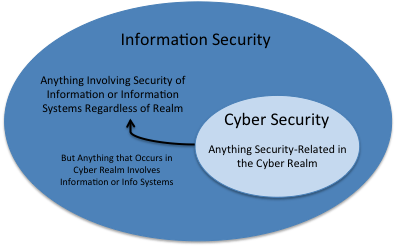
It Security Vs Cybersecurity Cybersecurity Comptia

Cyber Security Consultant Jobs Description Certification Salary More

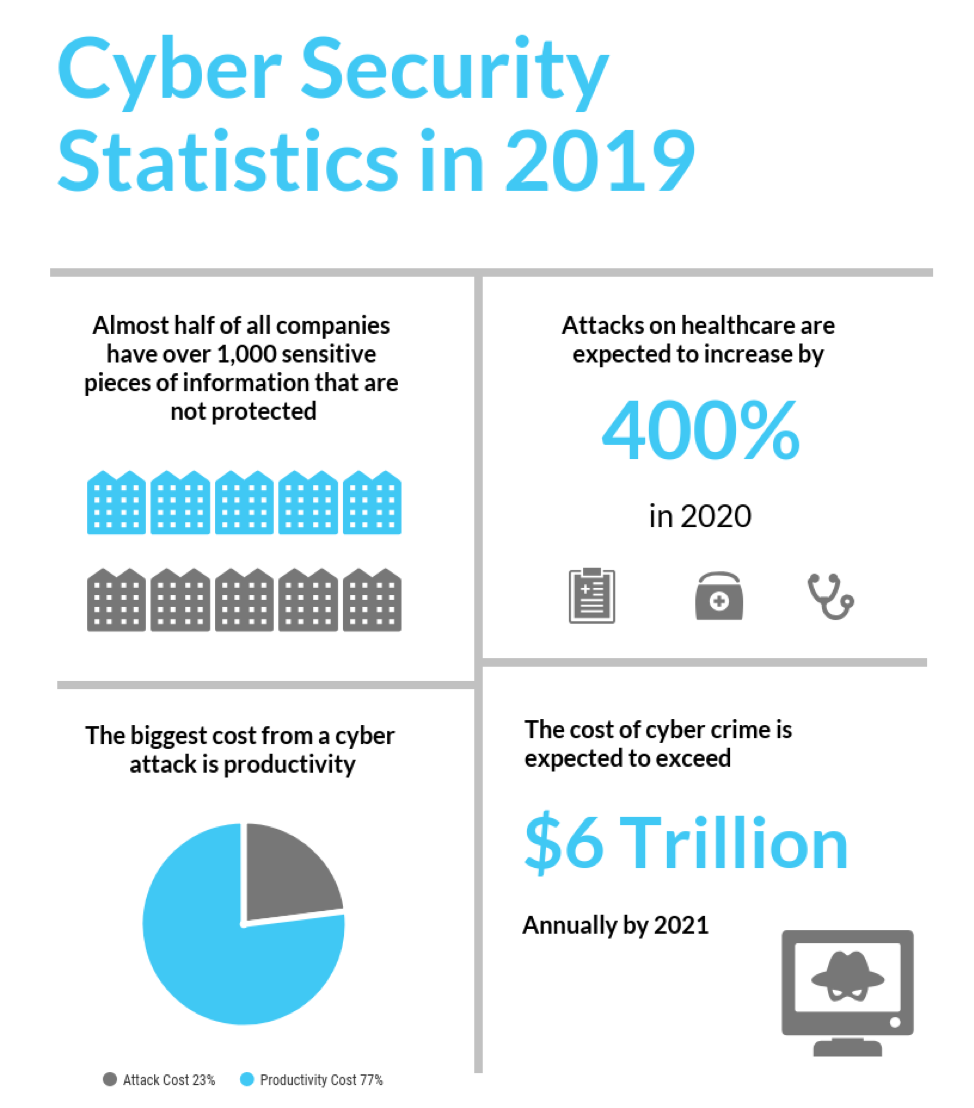
Infographic Here Are 10 Reasons Why Cyber Security Needs To Be Top Priority In 19 Link11

How To Better Integrate It Security And It Strategy Cio

Managed Security Services Irvine Ca Cybersecurity Vology

10 Common It Security Risks In The Workplace

It Security Policy Development Infosight
It Security Policy Template Free Privacy Policy

It S Time To Distinguish Information Security From It Security Nucleus Cyber

What Is Cyber Security Definition Types And User Protection Kaspersky

It Security Solutions Itg Information Technology Group

Guest Article How Employees Can Be Your Biggest Cyber Security Threat Uk Cyber Security Association
It Cyber Security Discovery Lansweeper It Discovery Software

3 Essential Components Of Your It Security Roadmap

What Is An It Security Audit The Basics Varonis

A Cto Guide Cyber Security Best Practice Tips Information Age
It Forensics And Security Auditing Software

Cloud Cape It Security Penetration Testing Vulnerability Management Managed Cloud

Cybersecurity Company I Affordable And Effective Cybersecurity Solutions Compliance And Consulting Services
What Is State Of The Art In It Security Enisa

It Security Management Tools Free Software Trial Solarwinds

How To Become An It Security Specialist Career Hq

Who Needs Cyber Security

Cyber Security Insurance On The Rise Aws Insurance Company

Few Execs Believe Healthcare It Security Tech Will Be Disruptive

Information Infrastructure Security Management Mindtree

Cyber Security And Executive Strategy Stanford Online

Industrial Cyber Security Why It Ot Collaboration Is No Longer An Option But A Necessity

No Shortcuts To Effective Cyber Security Amp Information Systems

7 It Security Tools From Microsoft Interlinked

A Quick Guide To Building An Efficient Cyber Security System Qualitest Group

The Top Ai Cyber Security Companies Information Age

How Much Does A Cyber Security Specialist Make

What Is An It Security Audit

Lack Of Internal It Security Expertise Requires Connected Threat Defense

It Security Roles And Responsibilities Simplilearn
Q Tbn 3aand9gctkgsamvacbnn5wci13xw035yqysly0ovt1wfoc55xga1mpajp Usqp Cau

Telekom Delivers It Security Deutsche Telekom

Should You Consider A Career As A Cyber Security Specialist
Q Tbn 3aand9gct9zgofihqfieo8juo8ro68yxwhhptcbiazdw9ijtnnvciipyt2 Usqp Cau

Cto Vs Ciso Who Should Have Ultimate Responsibility For Cyber Security

It Security Services Spending Worldwide 17 Statista

How To Practice Cybersecurity And Why It S Different From It Security Cso Online

7 Hidden Benefits Of It Security Compliance For Your Business
What Is Cyber Security A Beginner S Guide Rasmussen College

Why Segregation Of Duties Is Crucial For It Security Network Security
What Is Cyber Security Cybersec Threats Strategy Imperva
How Techology Is Revolutionizing It Security Software

What Is It Security Information Technology Security Cisco

How To Write An It Security Engineer Job Description Cso Online

It Security Law Enforcement Cyber Center
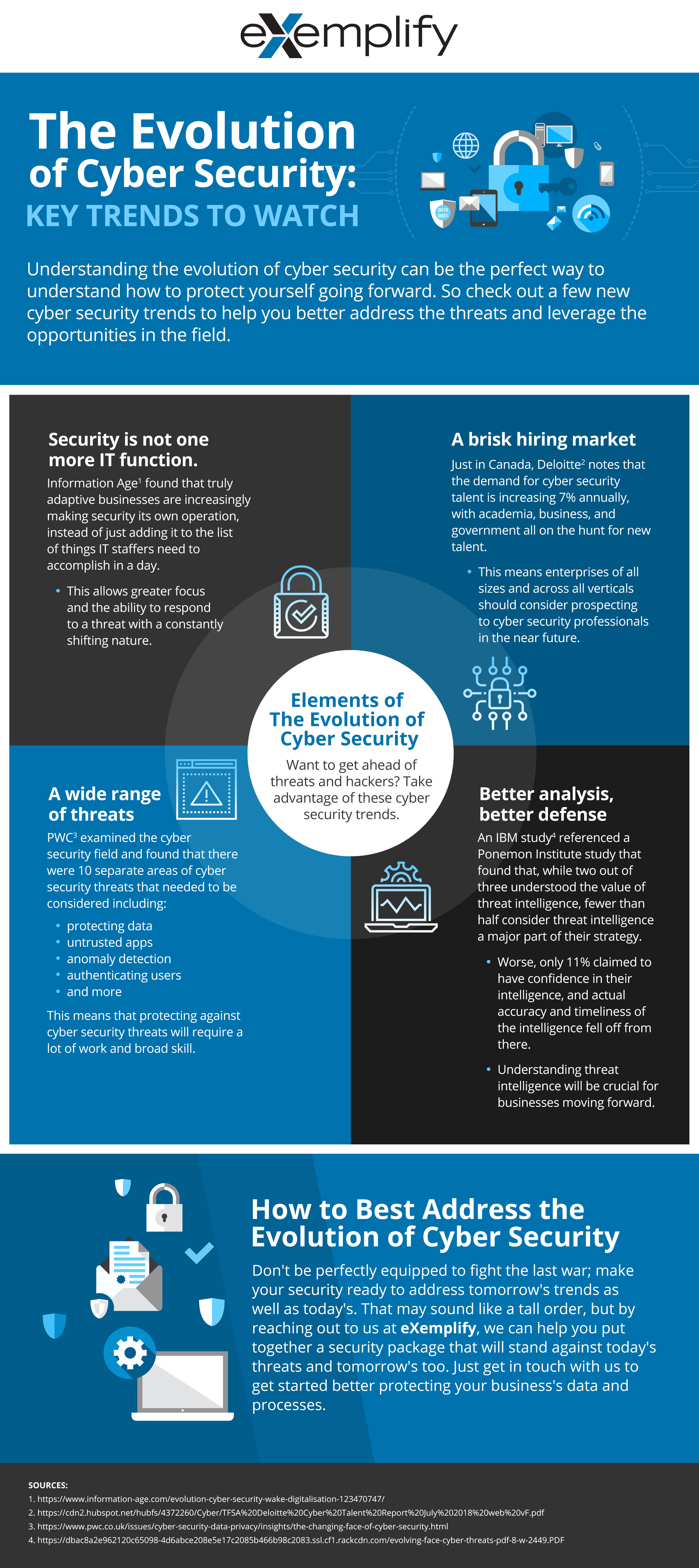
Infographic The Evolution Of Cyber Security Key Trends To Watch Exemplify More Than A Master Agent

10 Signs You Should Invest In It Security Excalibur Communications

Ship Cyber Security The Classnk Approach To Securing Onboard Systems

Matrix42 On Why Ueba Offers A Smart Approach To Enhanced It Security Intelligent Ciso

Cyber Security Training In Houston Cyber Security Certification Course

It Security Vs Cyber Security What Is The Difference Logsign

12 Top Tips For Cyber Security Context Information Security

What Is An It Security Audit Cheeky Munkey
1

Taking Responsibility For Cyber Security In A Truly Virtual World

Why Is Cyber Security Important In 19 Securityfirstcorp Com

It Security Services Connection

The Role Of An It Security Professional Technojobs Uk

What Project Managers Need To Know About Cyber Security

Cyber Security Specialist Job Description And Salary Fieldengineer

It Security Consulting Cyber Security Experts And Best Practices Sophos

New Cyber Security Threats Expected To Emerge In 19

Creating A Covid 19 Cyber Security Plan Connected It Blog

Is A Cyber Security Degree Worth It The Facts You Can T Ignore Rasmussen College

Webinar 3 Flaws With The Defense In Depth Security Model And How To Improve It

Bai Security Vulnerability Scanning It Security Assessment Vulnerability Management Vulnerability Assessment Tools Social Engineering Attacks Red Team Assessment It Cyber Security Risk Assessment What Is Social Engineering 847 410 8180 We

It Security Defense Against The Digital Dark Arts Coursera
What Are The Different Types Of It Security Rsi Security

Cybersecurity Atmosphere Chicago Cybersecurity

Cybersecurity Vs Information Security Is There A Difference Cloud Academy

Top 10 It Security Stories Of 18

Cyber Security Monitoring Network Monitoring Redscan
It Security Party Tricks Cybersecurity Insiders

4 Cyber Security Predictions For 18 Mobile Pensacola Bis Inc

Top Jobs In It Security It Security Job Designations Simpilearn

Cyber Security Lms Group

Macomb Community College It Network Security Professional Cybersecurity

Traditional It Security Vs Cloud Security Which Approach Is Right For Your Business Security Info Watch

Bank It Security Can Still Learn From 15 Top Takeaways Part 1 Thales Blog

The Rising Costs Of Cybersecurity Breaches Why It Security Is Doomed To Fail

The Importance Of Changing Your Cyber Security Mindset It World Canada News



